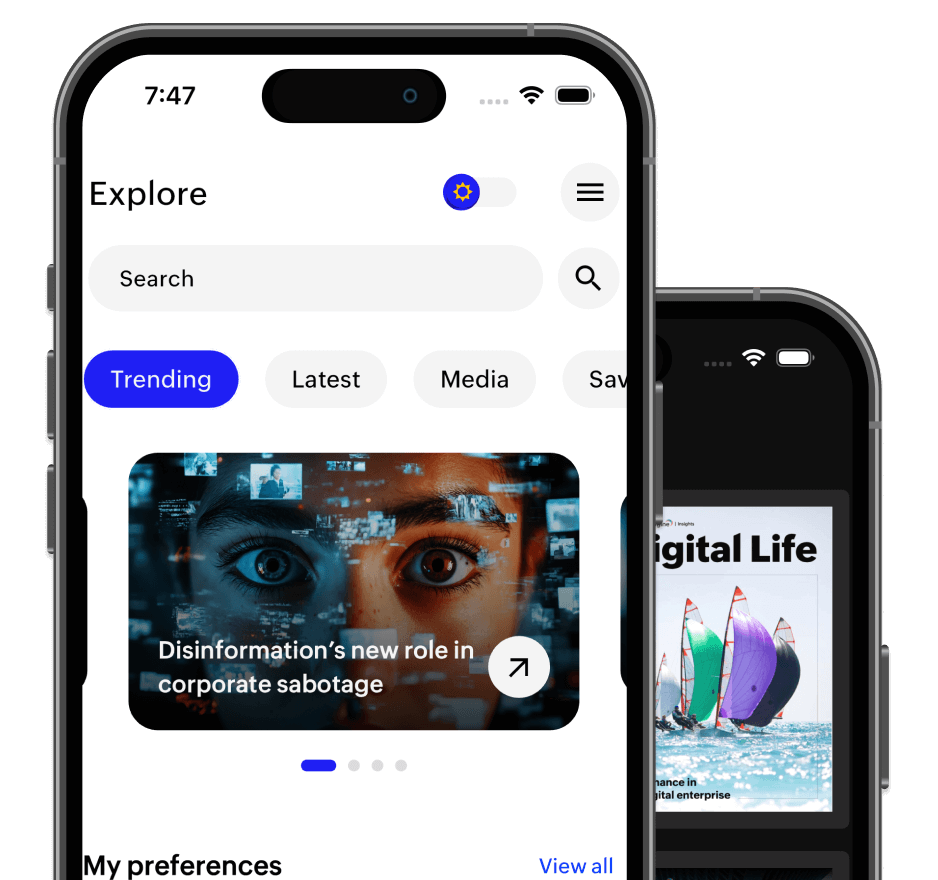
Featured
Artificial Intelligence
What is contextual decision intelligence and why should you care about it?
Here’s a scenario that should feel uncomfortably familiar. A loyal customer—let’s call her Sarah—has spent thousands of dollars on your platform over three years. She buys premium cookware, organic groceries, and the occasional kitchen
Articles
All